Tutorial
Updated
Patching DevMenu v6.0.1 to remove startup notification
This tutorial implies that you found DevMenu v6.0.1 on some other sites. With this forum rules, links to the required copyrighted material are forbidden.
Problem
This version of DevMenu checks the FW version and displays a message on its startup if it's higher than 6.0:
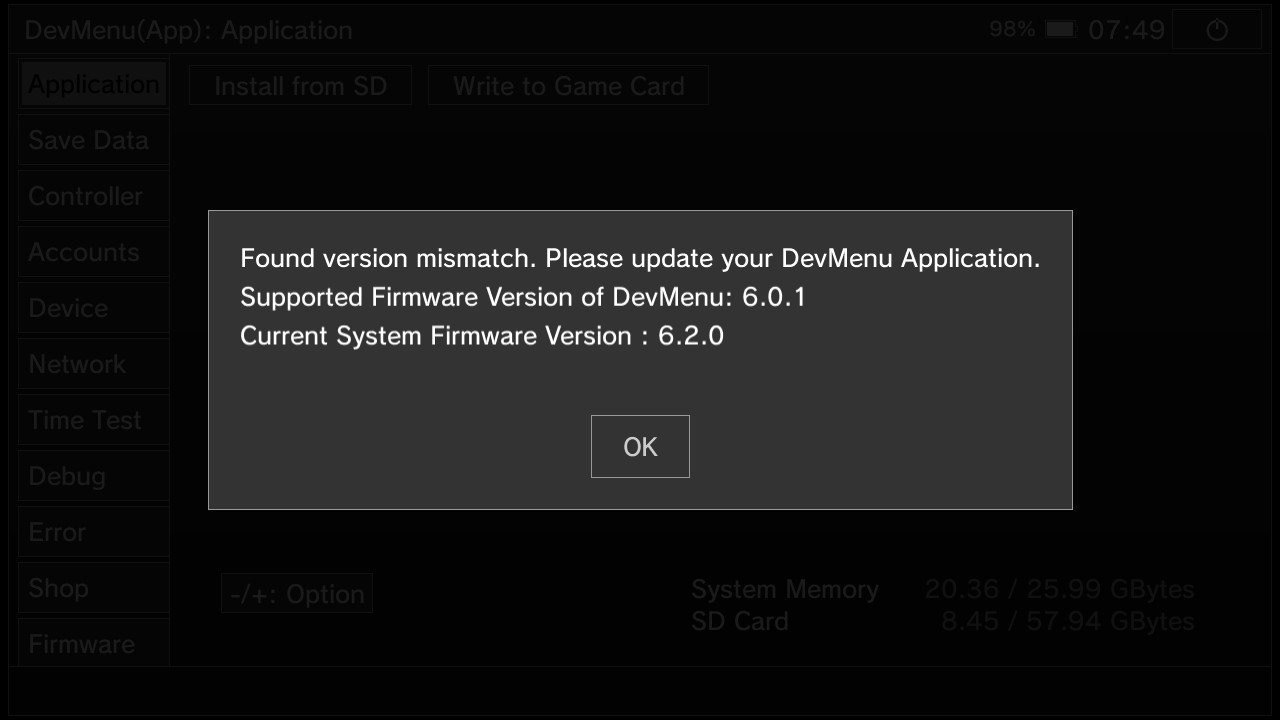
The purpose of this tutorial is to remove this panel.
Step 1 - Uncompress executable "main"
First, you need HacTool (https://github.com/SciresM/hactool/releases/tag/1.2.2) and the DevMenu executable "main". This executable should have the following properties:
If you got an NSP file (not a LayeredFS version), you must extract the NSP then the biggest NCA file with the following commands:
Step 2 - Patch executable "mainDec"
Open "mainDec" with an hexadecimal editor and replace the following bytes:
Now, you can replace "exefs/main" by the patched "mainDec" (rename it to "main").
If you were using a LayeredFS version of DevMenu, you don't have anything more to do. If it was an NSP version, you will have to rebuild the NSP using hacPack (https://github.com/The-4n/hacPack/releases/tag/v1.33).
Method used to find the patch
The executable was opened with IDA Pro 7.0 and the loader "nxo64" available here:
https://github.com/reswitched/loaders
There was a tracking on "Found version" string usage and it leads to the following code which gets and checks the firmware version:

Parts of this code have been replaced (thanks to http://armconverter.com website which was used to get equivalent binary code):

Those changes makes that, whatever the retrieved FW version, it's not checked anymore and conditions to avoid the notification panel are met.
Finaly, in order to make the executable accepted when it's launched, the NSO0 header has to be modified where the ".text" part hash is located (see https://switchbrew.org/wiki/NSO for further details).
Happy hacking!
Problem
This version of DevMenu checks the FW version and displays a message on its startup if it's higher than 6.0:
The purpose of this tutorial is to remove this panel.
Step 1 - Uncompress executable "main"
First, you need HacTool (https://github.com/SciresM/hactool/releases/tag/1.2.2) and the DevMenu executable "main". This executable should have the following properties:
Size: 5807948 bytes
SHA256: DD1BA1C488AF2CD6EAC1B1DCAAB143BF4F2003C0DB7B3FEA74113D80D25C274E
SHA256: DD1BA1C488AF2CD6EAC1B1DCAAB143BF4F2003C0DB7B3FEA74113D80D25C274E
If you got an NSP file (not a LayeredFS version), you must extract the NSP then the biggest NCA file with the following commands:
- hactool -t pfs0 -k keys.txt DevMenuApp.nsp --pfs0dir=extract
- hactool -k keys.txt --exefsdir=exefs --romfsdir=romfs BiggestFileInExtractDir.nca
- hactool -t nso0 -k keys.txt exefs/main --uncompressed=mainDec
Size: 15011376 bytes (14 MiB)
SHA256: E802D200640E0F0E4A86913BBB616C682DA0BE3D3F47A82F976F37FC4B3DF125
SHA256: E802D200640E0F0E4A86913BBB616C682DA0BE3D3F47A82F976F37FC4B3DF125
Step 2 - Patch executable "mainDec"
Open "mainDec" with an hexadecimal editor and replace the following bytes:
- Binary ARM code: E80345391F19007161000054E8074539 => 080080521F0100716100005408008052
- Hash check: EA43FE633F51336D3169BBFC70E280BAD95C4EF501AFC7E9D6C2310B745C8FBE => C1BEBE80DFE604D933F049090E95F5DFB60287E2CF65E46DFD70262954EB711D
Size: 15011376 bytes (14 MiB)
SHA256: 82F604C51F2B71D14571308DD5B87273BE1448F68432841BFB244986BA71CCBD
SHA256: 82F604C51F2B71D14571308DD5B87273BE1448F68432841BFB244986BA71CCBD
Now, you can replace "exefs/main" by the patched "mainDec" (rename it to "main").
If you were using a LayeredFS version of DevMenu, you don't have anything more to do. If it was an NSP version, you will have to rebuild the NSP using hacPack (https://github.com/The-4n/hacPack/releases/tag/v1.33).
Method used to find the patch
The executable was opened with IDA Pro 7.0 and the loader "nxo64" available here:
https://github.com/reswitched/loaders
There was a tracking on "Found version" string usage and it leads to the following code which gets and checks the firmware version:

Parts of this code have been replaced (thanks to http://armconverter.com website which was used to get equivalent binary code):

Those changes makes that, whatever the retrieved FW version, it's not checked anymore and conditions to avoid the notification panel are met.
Finaly, in order to make the executable accepted when it's launched, the NSO0 header has to be modified where the ".text" part hash is located (see https://switchbrew.org/wiki/NSO for further details).
Happy hacking!
Last edited by OperationNT,




